Hacked advertising platform sent users to exploit kit
A suspected malicious advertising attack turned out to be a much deeper compromise of an online advertising company, according to Trend Micro. The security …
SAP patches login flaw in ASE database
SAP patched a flaw on Thursday that could allow an attacker to take complete control over a database, according to security vendor Trustwave. The …
TrueCrypt security audit is good news, so why all the glum faces?
The ongoing audit of the TrueCrypt whole-disk encryption tool used by millions of privacy and security enthusiasts has reached an important milestone—a detailed review …
Over 100,000 devices can be used to amplify DDoS attacks via multicast DNS
Over 100,000 devices have a misconfigured service called multicast DNS that accepts requests from the Internet and can potentially be abused to amplify distributed …
Facebook tracks all site visitors, violating EU law, report says
Facebook tracks everyone who visits its site, including people who don’t have an account, and continues to track users and non-users who have opted …
Popular hotel Internet gateway devices vulnerable to hacking
Some Internet gateway devices commonly used by hotels and conference centers can easily be compromised by hackers, allowing them to launch a variety of …
A network error routed traffic for the UK’s nuclear weapons agency through Russian telecom
For the past week, something strange has been going on in the European internet. For five days, web traffic from Texas to certain addresses …
After Superfish-Lenovo incident, Facebook probes larger issue of SSL-sniffing adware
Last week, PC maker Lenovo was called out for shipping laptops with adware, called “Superfish,” pre-installed – an incident that led Facebook to investigate …
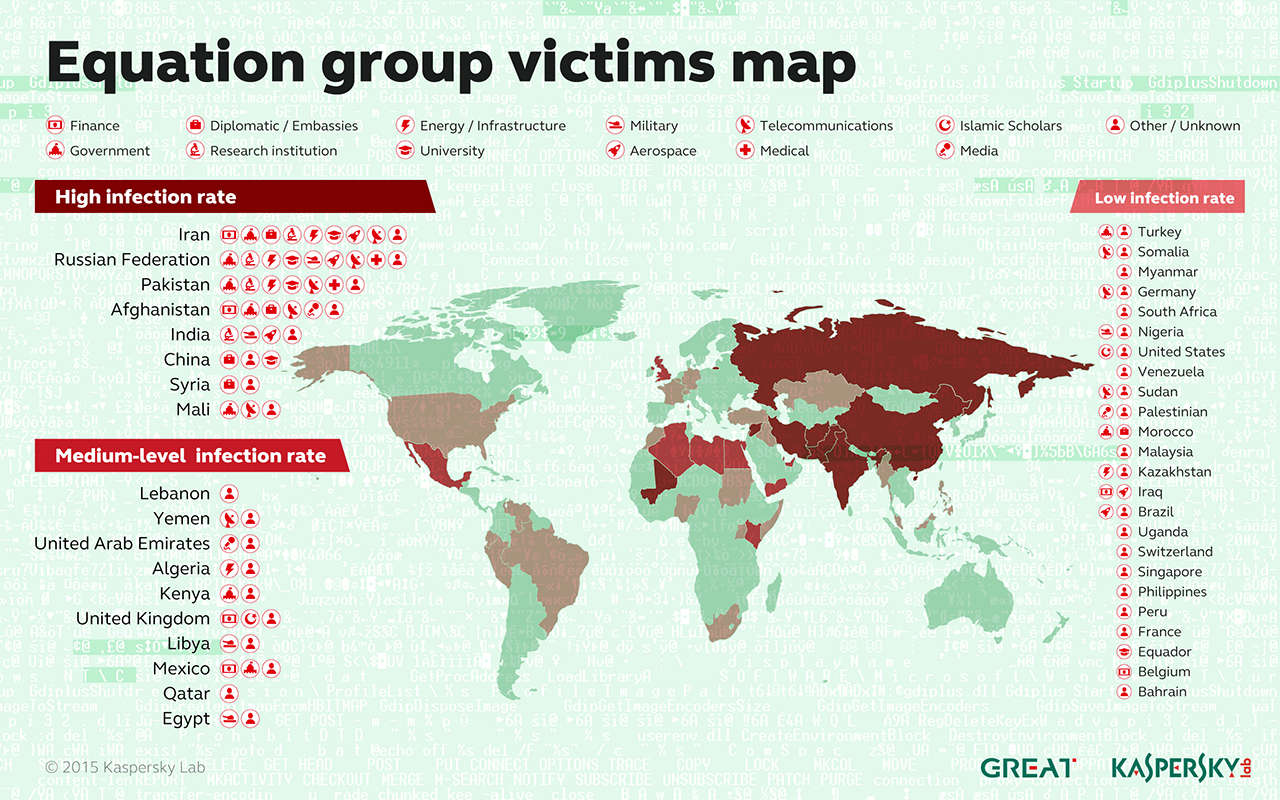
How “omnipotent” hackers tied to NSA hid for 14 years—and were found at last
In 2009, one or more prestigious researchers received a CD by mail that contained pictures and other materials from a recent scientific conference they …



Recent Comments